





Supports switching to any rear and front cameras, with manual controls for every camera.
With 10 composition grid overlays and 9 crop guides, combinable with each other.
Fast and simultaneous capture in JPEG and DNG formats, for complete flexibility in post-processing.
Zoom with pinch gesture, by using the shutter button as zoom rocker or use the volume keys!
The exposure compensation is always available by swiping on the viewfinder.
Many options like shutter, zoom, exposure, white balance or camera switching are assignable to the volume keys.



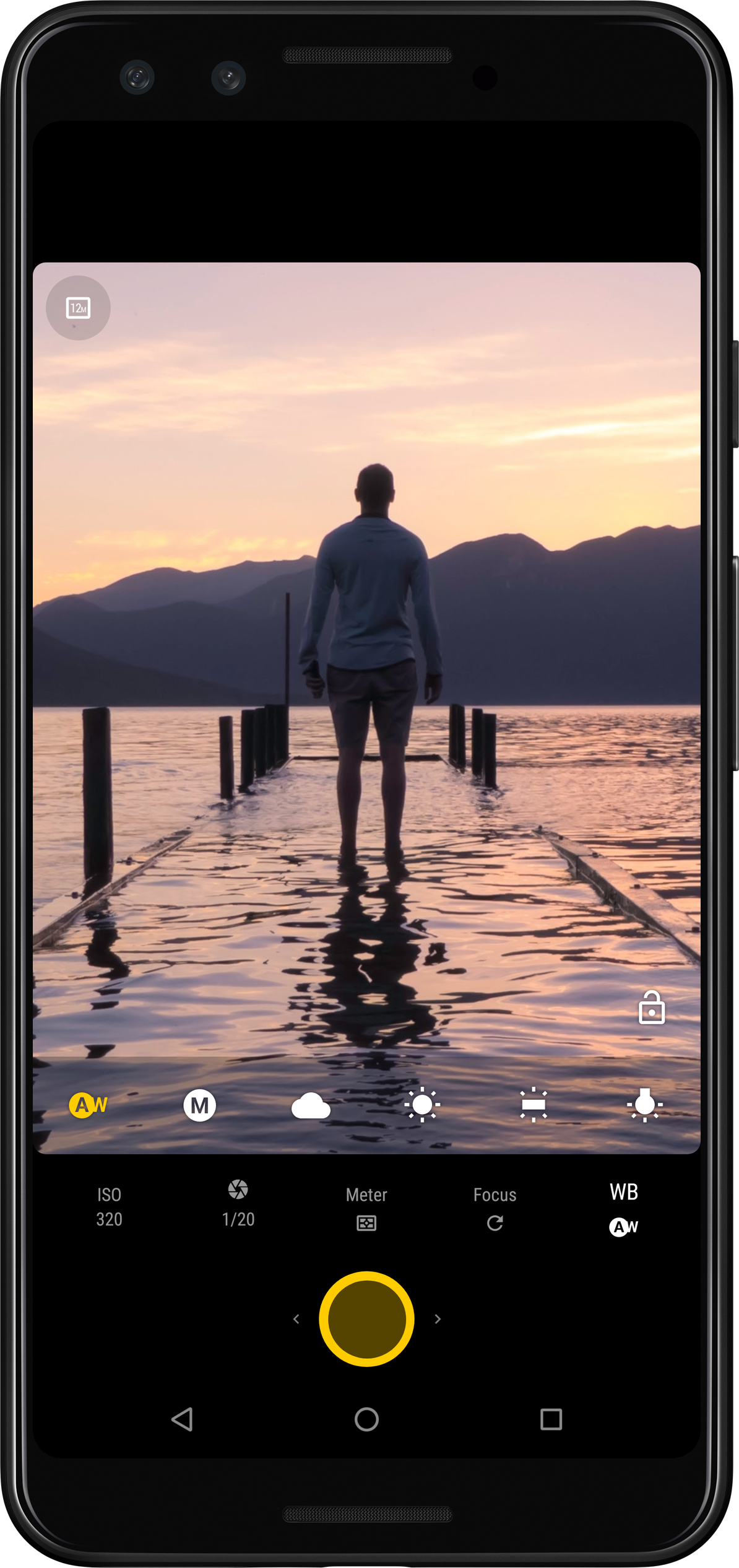

Complete control over the exposure, metering, white balance, focus and sensitivity.
Features like ISO, manual exposure or manual white balance require the device to support that. The value range of the adjustments is also device-dependent. Check the compatibility of your device.
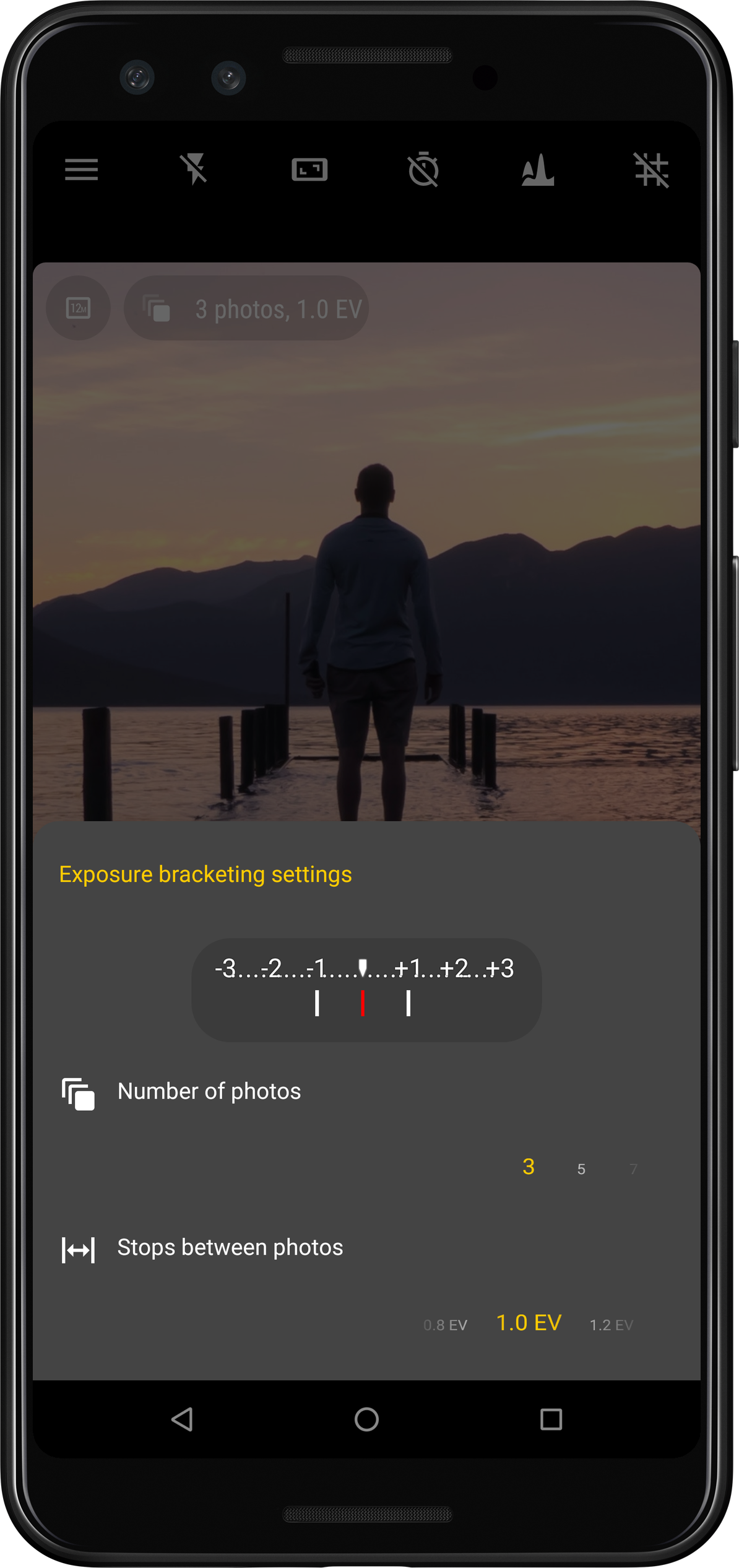
Take photos with multiple different exposures automatically.
New in version 5Now supports instantaneous capture even with JPEG+DNG on thousands of devices!

Capture picture series at regular intervals automatically (for instance timelapses or slow moving scenes)

Before we dive into the decryption process, it's essential to understand what KN5 files are and how they are encrypted. KN5 files are typically encrypted using a proprietary encryption algorithm that is specific to the software application that generated the file. This encryption algorithm uses a combination of techniques, such as symmetric key encryption and hashing, to protect the data stored in the file.
If you are unable to use software tools or online decryption services, you can try manual decryption techniques. However, this method requires advanced technical skills and knowledge of encryption algorithms. Additionally, manual decryption techniques can be time-consuming and may not always be successful. how to decrypt kn5 files
KN5 files are encrypted files that are generated by certain software applications, particularly those used for creating and editing 3D models and animations. These files are often used to store sensitive data, such as copyrighted content, and are therefore encrypted to prevent unauthorized access. However, there may be situations where you need to decrypt KN5 files, such as when you need to access data that is stored in these files or when you want to use the data in a different application. Before we dive into the decryption process, it's